Windows Has Built-In Ransomware Protection—Here’s How to Keep Your PC Safe
Ghana
4
Windows Has Built-In Ransomware Protection—Here’s How to Keep Your PC Safe
Unbeknownst to many Windows users, Microsoft offers built-in ransomware protection. Learn how to use the feature to protect your PC.

With Ransomware on the rise, individuals, businesses, schools, and corporations alike need to have layers of protection and a bit of awareness.
Unknown to many Windows users, Microsoft offers a built-in ransomware protection feature in Windows 10 and later versions to protect your PC. Here's how to use it.
How to Turn On Windows 10 Ransomware Protection
To access security, go to the start menu and type “Windows Security” in the search bar. Or you can go to “Settings”, click “Update & Security”, and select “Windows Security.” (If you can’t find the option, there’s always the search bar at the top of the window.)
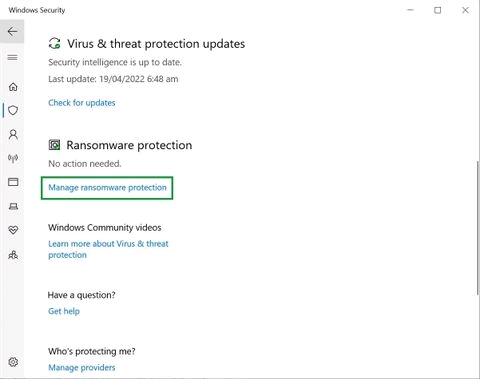
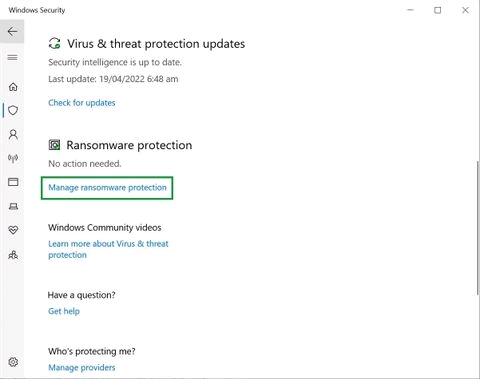
From there, go to “Virus and Threat Protection” and tap on “Manage Ransomware Protection" under the “Ransomware Protection” heading.
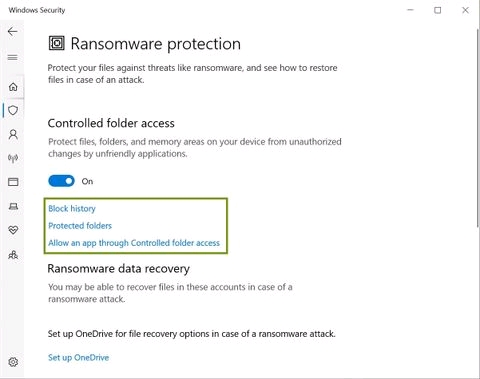
Once you open the “Ransomware Protection” page you’ll see an option called “Controlled Folder Access”.
When you turn it on, no unapproved apps can access or make changes to your files and data. This will prevent any malware from encrypting or deleting your data.
If you have third-party antivirus software installed and Windows real-time protection disabled, you won’t be able to access Ransomware Protection features and the Controlled Folder Access.
Customized Ransomware Protection
You can customize your options and choose the apps you want to allow while others remain blocked.
You can also add folders of your choice to the protected list. Three options appear as you switch on the Controlled Folder Access.
Block History
Block history gives you the list of apps that have tried to access your protected folders and were blocked.
If you’re having issues running certain apps after turning on “Controlled Folder Access”, you might want to check Block History to see if those were the ones blocked.
Protected Folders
When you go to “Protected Folders” you get a list of folders that blocked apps can’t access without permission. You can add more folders to this list by clicking the “+ Add Protected Folder” button and selecting folders in the File Explorer window that pops up right after.
You can navigate further and choose folders containing sensitive files, or data you can’t afford to lose. An example could be the Desktop folder because it’s not in the protected list by default.
Allow an App Through Controlled Folder Access
If you trust certain apps and don’t wish to block them, you can click on “Allow an app through Controlled Folder Access”.
From there, you can select “Recently Blocked Apps” if your app is in the block history. If it’s not there, you can find it by clicking on “Browse All Apps”.
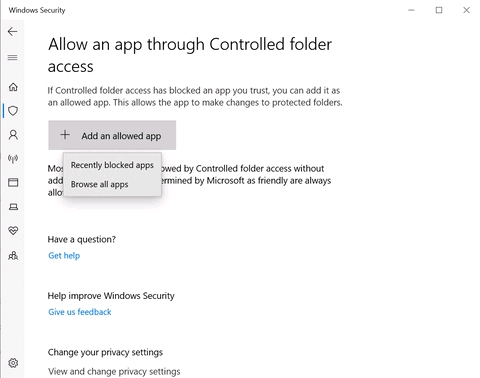
Go through the list of apps and click on the “+” button next to your preferred apps. This adds those apps to the white list or the list of apps allowed access to your data.
OneDrive Backup
If you’re a registered Microsoft user, you can get a cloud backup of your files on OneDrive.
Go to the search bar in the Start Menu, type “OneDrive” and open it. Sign in using your credentials, and it will walk you through the process of saving and sorting your folders online and offline.
When you sync OneDrive to your computer, you can access your files from anywhere.
More Tips on How to Protect Against Ransomware

While Windows offers two layers of protection–Anti-malware scans and Ransomware Protection features–it won’t be enough if you’re not vigilant.
Here’s a list of preventative measures you can take against malware or ransomware attacks.
Create Back-Ups
Take multiple online and offline backups through cloud services and external storage devices. In case hackers know about any of your backups, you’ll have others to fall back onto. When choosing a cloud service, make sure it’s synced with your devices or automatically updates backup.
All online backups can be accessed, and the work hackers are willing to put in depends on what your data is worth. Therefore, we also recommend backing up your data to external storage devices that cannot be accessed by hackers.

Separate Your Devices
The work-from-home culture has made a lot of us use the same devices for work and personal use. It feels convenient but it can be dangerous.
Your personal data can fall into the hands of ransomware attackers intending to cease your business. Such mishaps can lead to greater loss, more blackmail, and loss of files having sentimental value.
Update Your Software and Apps
Malware is evolving. Almost every update in apps and software is like a security patch on a newfound loophole.
If you don’t update your Windows, software, and apps regularly, chances are that you’re leaving those loopholes open to be exploited.
Never Download These Things
An attachment sent from an unknown email
Files sent by strangers through SMS or social media
So-called documents with the .exe or .msi extensions
You can check a file’s extension by right-clicking on it, selecting Properties, and looking at the details mentioned under the “Type Of File” heading.
Any suspicious extension that doesn’t align with what the sender claims it to be is a no-go area. That's why getting familiar with different kinds of extensions can go a long way.

Don’t Click on Shady Links
You’ll come across all kinds of links online. Some of them end up being scripts that trigger actions on your behalf like forwarding something to all your contacts or granting permissions on your behalf.
Other links can be spyware or other malware. None of these are good news. You must know how to spot it.
Don’t click on links that don’t add up with the context. Check URL addresses before clicking. Although URLs can be shortened or renamed, checking them is still a good practice.
What to Do in Case of a Ransomware Attack

No system is foolproof and we all make mistakes. If you end up in a situation where your device or PC is infected by ransomware, here’s what to do:
Disconnect your device from shared networks
Report the ransomware to law enforcement authorities
Disconnect backups till a thorough system cleanup
Look for decryption tools
Reset passwords
Stay Safe and Stay Alert
Online extortion sounds scary for many vulnerable individuals and small businesses who cannot invest much in cyber-security.
Simple measures like keeping your software up to date, using windows built-in ransomware protection, being aware of best practices, and staying vigilant can keep you secure.
#TechTipsPurple
Unbeknownst to many Windows users, Microsoft offers built-in ransomware protection. Learn how to use the feature to protect your PC.

With Ransomware on the rise, individuals, businesses, schools, and corporations alike need to have layers of protection and a bit of awareness.
Unknown to many Windows users, Microsoft offers a built-in ransomware protection feature in Windows 10 and later versions to protect your PC. Here's how to use it.
How to Turn On Windows 10 Ransomware Protection
To access security, go to the start menu and type “Windows Security” in the search bar. Or you can go to “Settings”, click “Update & Security”, and select “Windows Security.” (If you can’t find the option, there’s always the search bar at the top of the window.)
From there, go to “Virus and Threat Protection” and tap on “Manage Ransomware Protection" under the “Ransomware Protection” heading.
Once you open the “Ransomware Protection” page you’ll see an option called “Controlled Folder Access”.
When you turn it on, no unapproved apps can access or make changes to your files and data. This will prevent any malware from encrypting or deleting your data.
If you have third-party antivirus software installed and Windows real-time protection disabled, you won’t be able to access Ransomware Protection features and the Controlled Folder Access.
Customized Ransomware Protection
You can customize your options and choose the apps you want to allow while others remain blocked.
You can also add folders of your choice to the protected list. Three options appear as you switch on the Controlled Folder Access.
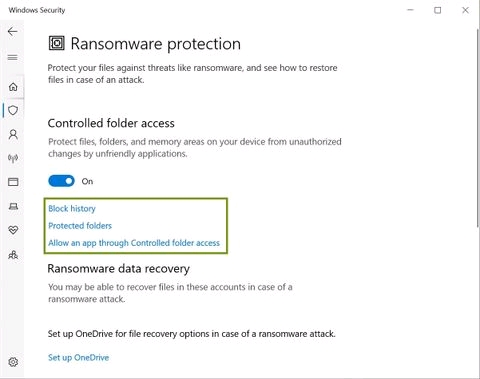
Block History
Block history gives you the list of apps that have tried to access your protected folders and were blocked.
If you’re having issues running certain apps after turning on “Controlled Folder Access”, you might want to check Block History to see if those were the ones blocked.
Protected Folders
When you go to “Protected Folders” you get a list of folders that blocked apps can’t access without permission. You can add more folders to this list by clicking the “+ Add Protected Folder” button and selecting folders in the File Explorer window that pops up right after.
You can navigate further and choose folders containing sensitive files, or data you can’t afford to lose. An example could be the Desktop folder because it’s not in the protected list by default.
Allow an App Through Controlled Folder Access
If you trust certain apps and don’t wish to block them, you can click on “Allow an app through Controlled Folder Access”.
From there, you can select “Recently Blocked Apps” if your app is in the block history. If it’s not there, you can find it by clicking on “Browse All Apps”.
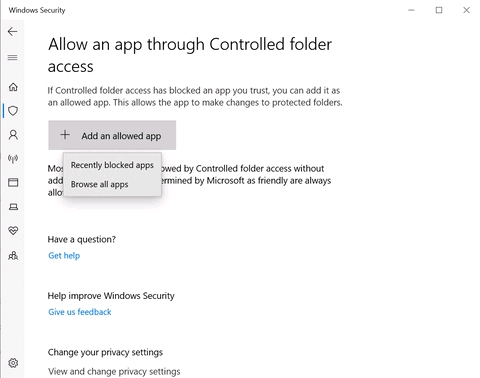
Go through the list of apps and click on the “+” button next to your preferred apps. This adds those apps to the white list or the list of apps allowed access to your data.
OneDrive Backup
If you’re a registered Microsoft user, you can get a cloud backup of your files on OneDrive.
Go to the search bar in the Start Menu, type “OneDrive” and open it. Sign in using your credentials, and it will walk you through the process of saving and sorting your folders online and offline.
When you sync OneDrive to your computer, you can access your files from anywhere.
More Tips on How to Protect Against Ransomware

While Windows offers two layers of protection–Anti-malware scans and Ransomware Protection features–it won’t be enough if you’re not vigilant.
Here’s a list of preventative measures you can take against malware or ransomware attacks.
Create Back-Ups
Take multiple online and offline backups through cloud services and external storage devices. In case hackers know about any of your backups, you’ll have others to fall back onto. When choosing a cloud service, make sure it’s synced with your devices or automatically updates backup.
All online backups can be accessed, and the work hackers are willing to put in depends on what your data is worth. Therefore, we also recommend backing up your data to external storage devices that cannot be accessed by hackers.

Separate Your Devices
The work-from-home culture has made a lot of us use the same devices for work and personal use. It feels convenient but it can be dangerous.
Your personal data can fall into the hands of ransomware attackers intending to cease your business. Such mishaps can lead to greater loss, more blackmail, and loss of files having sentimental value.
Update Your Software and Apps
Malware is evolving. Almost every update in apps and software is like a security patch on a newfound loophole.
If you don’t update your Windows, software, and apps regularly, chances are that you’re leaving those loopholes open to be exploited.
Never Download These Things
An attachment sent from an unknown email
Files sent by strangers through SMS or social media
So-called documents with the .exe or .msi extensions
You can check a file’s extension by right-clicking on it, selecting Properties, and looking at the details mentioned under the “Type Of File” heading.
Any suspicious extension that doesn’t align with what the sender claims it to be is a no-go area. That's why getting familiar with different kinds of extensions can go a long way.

Don’t Click on Shady Links
You’ll come across all kinds of links online. Some of them end up being scripts that trigger actions on your behalf like forwarding something to all your contacts or granting permissions on your behalf.
Other links can be spyware or other malware. None of these are good news. You must know how to spot it.
Don’t click on links that don’t add up with the context. Check URL addresses before clicking. Although URLs can be shortened or renamed, checking them is still a good practice.
What to Do in Case of a Ransomware Attack

No system is foolproof and we all make mistakes. If you end up in a situation where your device or PC is infected by ransomware, here’s what to do:
Disconnect your device from shared networks
Report the ransomware to law enforcement authorities
Disconnect backups till a thorough system cleanup
Look for decryption tools
Reset passwords
Stay Safe and Stay Alert
Online extortion sounds scary for many vulnerable individuals and small businesses who cannot invest much in cyber-security.
Simple measures like keeping your software up to date, using windows built-in ransomware protection, being aware of best practices, and staying vigilant can keep you secure.
#TechTipsPurple
Comments (4)
0/500
New Comments(4)
Boysondntz5
A S Dabo
awesome
leticia tave
cool
¢ountdowπ | $po®tz
nice
cool